A Summary of Smartsheet Future of Work Management Report 2023 The emergence of ChatGPT serves as a reminder that the world is undergoing a transformation and advancing towards the age of AI. The crucial question that remains unanswered is whether human beings will be replaced by AI in the future. To prevent this catastrophic outcome, we must strive to keep pace with the world's evolution by adopting new technological tools and integrating them into our daily lives. This not only ensures our survival in an AI-dominated world but also facilitates our productivity and adaptability in a rapidly changing environment.
Recently I came across this webpage: How Much Is “The Way We’ve Always Done It” Costing You?. In this page, there is a cost calculator to determine how much time and money you and your team waste on inconsistent processes, status meetings, and tedious, manual work.
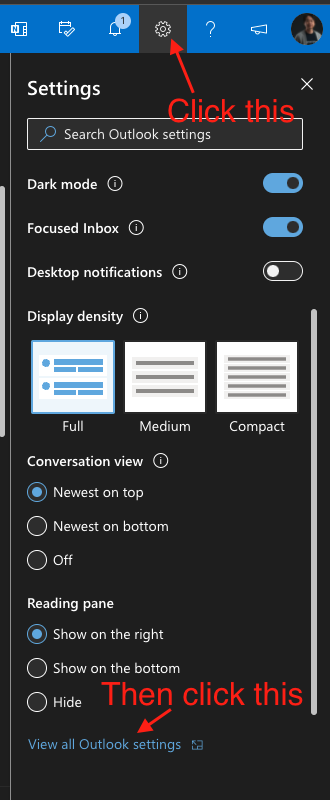
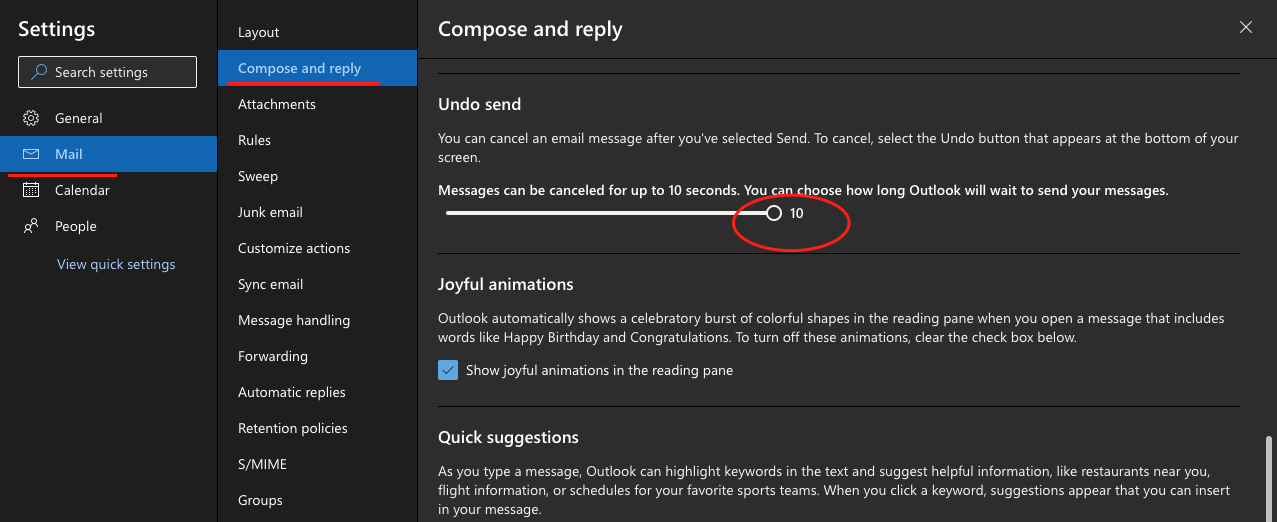
You may access the cost calculator here: https://www.smartsheet.com/status-quo-cost-calculator Immediately, I keyed in the information to the best of my knowledge and was so amazed to see the time I spent in each of those areas: work processes, status meetings, manual work. Here is a summary of 57Network’s result. Have you ever sent out an email accidentally and unable to undo it? The good news is, you can change the setting to delay the email sending even you clicked the send button. Once you set it, you can undo email sending within a short seconds, this could give you a short windows of time to undo your email sending. NOTE : However, you are not able to undo it once your email has been sent out successfully, and you have to work around it by sending another email to inform your recipient regarding your mistake or whatsoever reasons. Step 1 : click the setting icon at the top right section of your Outlook Web Step 2 : Under Mail > Compose and reply > under Undo Send, toggle the time to the longest value Done!
Base on Smartsheet Report on Collaboration Beyond Communication, we have prepared an infographic for your easy reference.
You can assessed the full report here. Change is indeed a part of life as the saying goes, "the only thing constant is change." Since the pandemic started in early 2020, we are seeing changes taking place in every sphere of life. How are you coping with change? How is your team coping with change? Schedule an appointment with 57Network to find out more about how Smartsheet can help you streamline workplace collaboration and support a dynamic workforce. We are now in the last quarter of 2020. It has been a challenging and tough year. We have seen and heard from many who rose above this unprecedented circumstances.
Nobody is prepared for this global pandemic. What initially thought to be an outbreak in a city called Wuhan had in no time spread throughout the world. City after city are in lockdown. Lives, businesses, economy and many aspects are impacted. Like it or not, we have to make new adjustments. I oftentimes find myself forgot to put on my mask when I got out of my car. So, I decided to put it on the moment I leave my house, get in the car and get out of the car. Instead of "when can I meet you?", the new question is "when can we zoom?" Instead of planning for our weekly grocery shopping, we find ourselves reviewing every available merchant online to decide where should we purchase our meat, vegetables, fruits and other essential items from. So, how about our work? Will it ever be the same again? How many of you have been attending meeting after meeting over zoom just to get updates and realign with your team? Is this the effective use of your time? You want to get more out of your workday so you can achieve everything you set out to do. But with never ending email, multiple chat apps, and impossible-to-find information, it’s hard to know whether you’re working on the most important things — or if you’re even getting anything done. You need a way to work that works for you — and that can adapt as your tasks, projects, and programs change. One that enables real collaboration, gives you the information you need to be successful, and frees you up to innovate and drive better results. Download this free report to learn how you can take control of the way you work and achieve more by solving for these common issues at work:
Notifications were created to help keep us on track and in the know, but as with anything in life, they can be too much of a good thing. Being interrupted with a constant stream of notifications can often derail productivity. After a notification forces a worker to switch between tasks, it can take them about 23 minutes to get back to the task at hand, according to Harvard Business Review. It can be challenging for teams to weave through the noise and make sure they are paying attention to the key information related to their work. Use these four tips to help improve your experience with automated alerts and requests from Smartsheet: 1. Personalize the Frequency 2. Add Context to Subject Lines 3. Only Include Relevant Fields 4. Choose How You Want to Receive Them The short-term benefits of automating repetitive, manual workflows are well known: saving time, saving money, and increasing efficiency. But there are lesser-known, long-term benefits of automation, too, and they can have a profound and lasting effect on the success of your business. Here are three ways in which automating processes can transform your business for the long haul. 1. Focus Employees on Innovation 2. Reduce Risk 3. Make Better Decisions It’s important for workers to have the opportunity to improve work processes and increase efficiency so that businesses can consistently move faster and innovate. Automation can help free workers up to focus on more valuable, high-impact tasks that help propel their teams, departments, and organizations forward.
|
|||||||
|
Care line: +603-9212 0157
|
Leave us your inquiry |
|
This company is registered with the Ministry of Finance, Malaysia.
Equip your organisation with digital solutions & training that inspire innovation and joy at work. Copyright © 2024 57Network Consultancy Sdn. Bhd. Company Registration number : 202001020346 (1376666-K) All rights reserved. |